MDATP – Automatically isolating machines
Microsoft Defender Advanced Threat Protection is an EDR tool, which stands for Endpoint Detection and Response. Today I want to focus on the Response part.
When investigating an incident or alert in MDATP, you might come to the conclusion that it is best to isolate the machine from the network in order to prevent a worm from spreading. Although doing this by hand gives you the best control, there is a small delay between the alert arising and someone triggering the isolate action. To shorten this delay, I have previously written about how to get alerts via SMS and Push Notification in addition to email. But even then, someone still needs to be notified, open the portal, investigate the alert and then decide to perform the isolation.
Luckily, we can use Microsoft Flow to automate this process. At least, we can isolate a machine when an alert occurs.
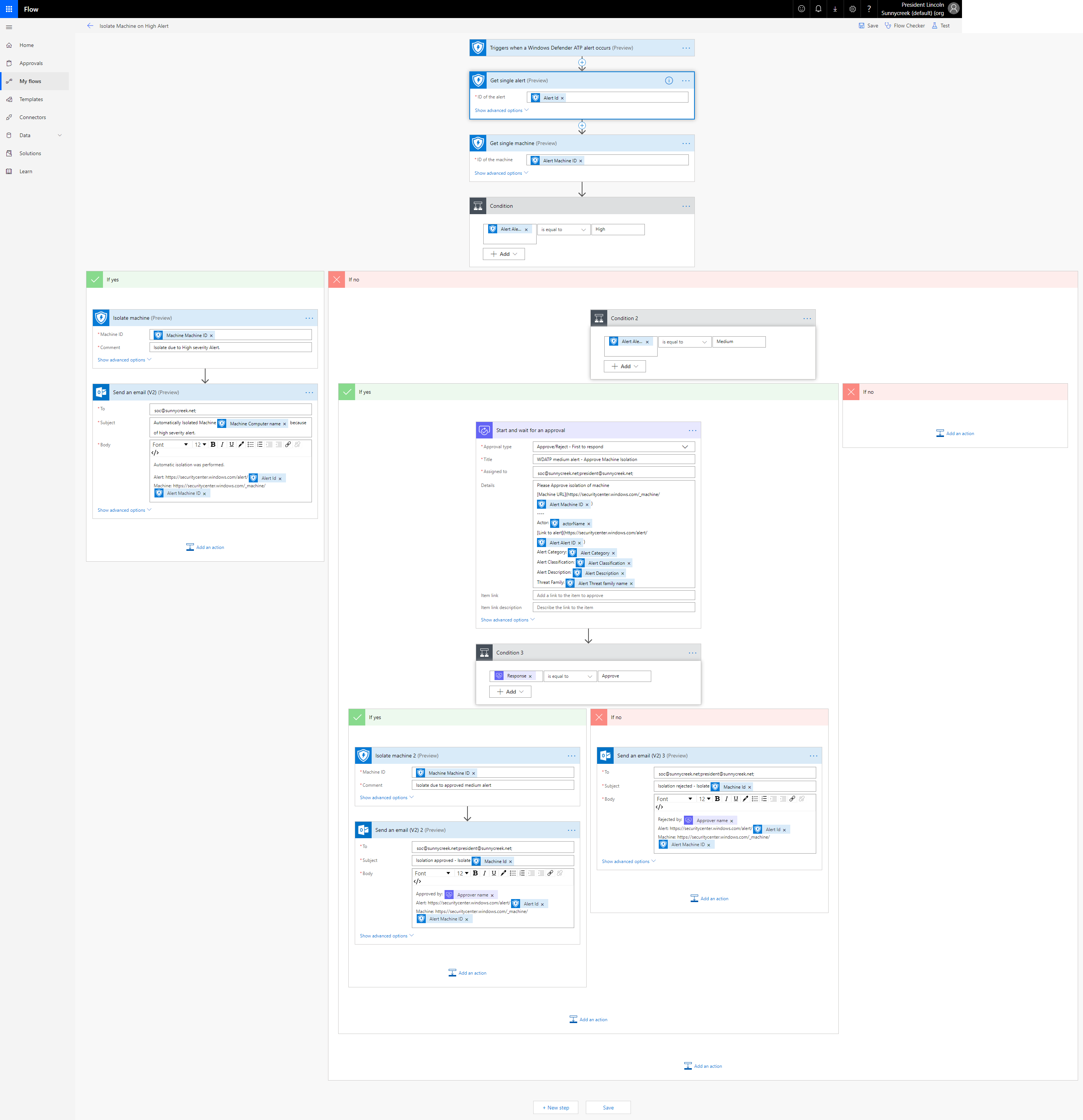
First, I want to provide the logic behind the Flow as pseudo code. This makes it much easier to understand what I am trying to achieve.
if (Severity == High) {
IsolateMachine()
SendMail(Automatically isolated machine)
} else {
if (Severity == Medium) {
StartAndWaitForApproval()
if (Response == Approve) {
IsolateMachine()
SendMail(Isolated machine after approval)
} else {
SendMail(Machine isolation not approved)
}
}
}
The logic behind this is really simple. Let me break it down:
- Every high severity alert will always automatically isolate the machine – No interaction required
- Every medium severity alert will trigger an approval email which can be approved or rejected – Isolation only if someone approves
- Nothing happens on low or informational alerts
This is only of the many possibilities. You can adapt the functionality to model whatever requirement you are facing.
Lets start with the Microsoft Flow portal (https://flow.microsoft.com). Sign in and select My Flows.
- Click on New and select Automated – from blank.
- Give it a name and search for Windows Defender ATP in the trigger field.
- Select Triggers when a Windows Defender ATP alert occurs and click Create.
Note: You might have to activate the connector first because it is a Premium connector. More info on the connectors capabilities can be found here.
Alternatively, I exported the Flow to JSON and uploaded it to my Github here so you can simply import it in Flow. Just make sure to change the email address.
I recommend always starting with Get single Alert and Get single Machine. They provide more data like severity and machine name.
From here on it is up to you how you want your logic to be. I have implemented my scenario as seen in the screenshot. (Click to zoom or right click – open in new tab here for the original)
Note: The approval does not seem to work when using it with a shared mailbox; the response will not be recorded.
The interface is intuitive and you should be able to figure out how to rebuild the Flow by using the picture as a blueprint.
Automatically isolating machines can potentially create scenarios which are not ideal. However, a high alert in MDATP really indicates something bad is going on. For example, we have observed mimikatz (or mimikatz related alerts like pass-the-ticket) in a lot of high severity alerts. Therefore I think this is a good starting point. As always, be sure to test and evaluate based on your needs.