Preventing administrative users to change critical network settings in an Azure hub-spoke topology
An Azure hub-spoke topology enables a company to use infrastructure as a service without losing control of the network flow. This is particularly important if you have business users with their own subscription (which I support) and the services in this spoke needs access to on-premises resources via a vpn gateway (e.g. site-2-site vpn).
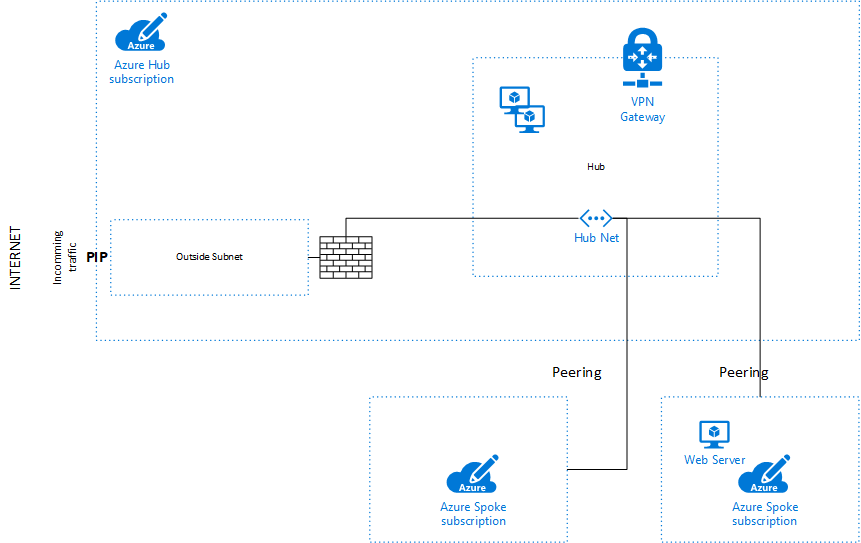
To prevent the business users from changing the network settings in the prepared spoke subscriptions, it’s necessary to give them the right role in Azure. I tried some of the built-in role but I didn’t find one which allows nearly everything except deleting routing rules, edit subnets, etc. For example: If you deny access to the spoke vnet itself, the user can no longer create a vm, because the nic of a vm needs to join a vnet/subnet (which the user needs access to).
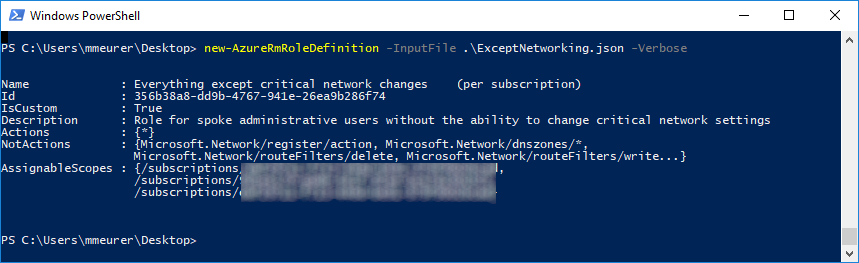
So, I built a custom role which allows this. You can import this custom role with powershell:
|
1
2
|
Get-AzureRmSubscription # login to AzureNew-AzureRmRoleDefinition -InputFile .\ExceptNetworking.json |
Now you can add this role for your business user to the root to your subscription. The user can do nearly everything without changing your network setting.
The definition for ExceptNetworking.json:
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
|
{ "Name": "Everything except critical network changes (per subscription)", "Id": "6ffa1df5-20ef-4926-8bf9-6e44a5315b9d", "IsCustom": true, "Description": "Role for spoke administrative users without the ability to change critical network settings", "Actions": [ "*" ], "NotActions": [ "Microsoft.Network/register/action", "Microsoft.Network/dnszones/*", "Microsoft.Network/routeFilters/delete", "Microsoft.Network/routeFilters/write", "Microsoft.Network/routeFilters/rules/write", "Microsoft.Network/routeFilters/rules/delete", "Microsoft.Network/virtualNetworks/write", "Microsoft.Network/virtualNetworks/peer/action", "Microsoft.Network/virtualNetworks/virtualNetworkPeerings/write", "Microsoft.Network/virtualNetworks/virtualNetworkPeerings/delete", "Microsoft.Network/virtualNetworks/subnets/write", "Microsoft.Network/virtualNetworks/subnets/delete", "Microsoft.Network/localnetworkgateways/write", "Microsoft.Network/expressRouteCircuits/write", "Microsoft.Network/expressRouteCircuits/delete", "Microsoft.Network/expressRouteCircuits/peerings/write", "Microsoft.Network/expressRouteCircuits/peerings/delete", "Microsoft.Network/expressRouteCircuits/authorizations/write", "Microsoft.Network/expressRouteCircuits/authorizations/delete", "Microsoft.Network/connections/write", "Microsoft.Network/connections/sharedKey/read", "Microsoft.Network/applicationGateways/write", "Microsoft.Network/routeTables/write", "Microsoft.Network/routeTables/delete", "Microsoft.Network/routeTables/routes/write", "Microsoft.Network/routeTables/routes/delete", "Microsoft.Authorization/roleDefinitions/write", "Microsoft.Authorization/roleDefinitions/delete", "Microsoft.Authorization/policyDefinitions/write", "Microsoft.Authorization/policyDefinitions/delete", "Microsoft.Authorization/roleAssignments/write", "Microsoft.Authorization/roleAssignments/delete" ], "AssignableScopes": [ "/subscriptions/<Subscription 1>", "/subscriptions/<Subscription 2>", "/subscriptions/<Subscription 3>" ]} |
The “id” is a random guid. Add the subscription id’s you want to use with this role to “AssignableScopes”.
